Service Mesh with Istio: Complete Kubernetes Guide
Master Istio service mesh for Kubernetes. Learn traffic management, security, observability, and build resilient microservices architectures.
Moshiour Rahman
Advertisement
What is Istio?
Istio is a service mesh that provides traffic management, security, and observability for microservices. It handles cross-cutting concerns without changing application code.
Architecture Overview
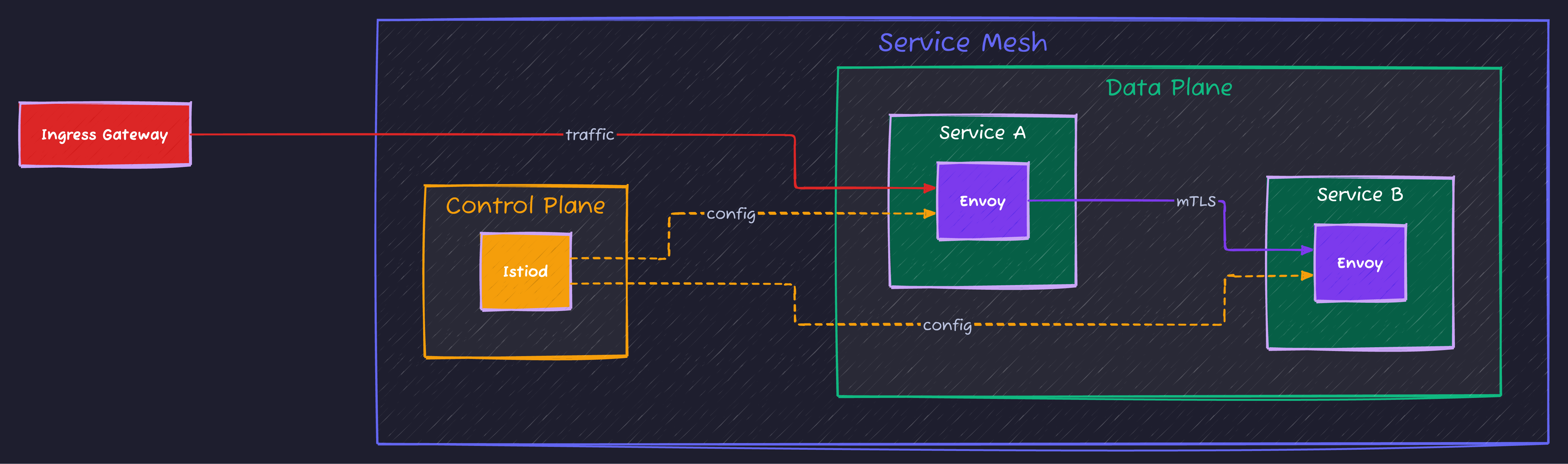
The Sidecar Pattern
Istio works by injecting a proxy (Envoy) next to every application container.
Service Mesh Benefits
| Feature | Description |
|---|---|
| Traffic Management | Routing, load balancing |
| Security | mTLS, authorization |
| Observability | Metrics, tracing |
| Resilience | Retries, circuit breakers |
Getting Started
Installation
# Download Istio
curl -L https://istio.io/downloadIstio | sh -
cd istio-*
export PATH=$PWD/bin:$PATH
# Install Istio
istioctl install --set profile=demo -y
# Enable sidecar injection
kubectl label namespace default istio-injection=enabled
# Verify installation
kubectl get pods -n istio-system
istioctl verify-installInstall Addons
# Prometheus, Grafana, Kiali, Jaeger
kubectl apply -f samples/addons
# Access dashboards
istioctl dashboard kiali
istioctl dashboard grafana
istioctl dashboard jaegerTraffic Management
Virtual Services
apiVersion: networking.istio.io/v1beta1
kind: VirtualService
metadata:
name: my-service
spec:
hosts:
- my-service
http:
- match:
- headers:
user-agent:
prefix: "Mozilla"
route:
- destination:
host: my-service
subset: v2
- route:
- destination:
host: my-service
subset: v1Destination Rules
apiVersion: networking.istio.io/v1beta1
kind: DestinationRule
metadata:
name: my-service
spec:
host: my-service
trafficPolicy:
connectionPool:
tcp:
maxConnections: 100
http:
h2UpgradePolicy: UPGRADE
http1MaxPendingRequests: 100
http2MaxRequests: 1000
loadBalancer:
simple: ROUND_ROBIN
subsets:
- name: v1
labels:
version: v1
- name: v2
labels:
version: v2
trafficPolicy:
loadBalancer:
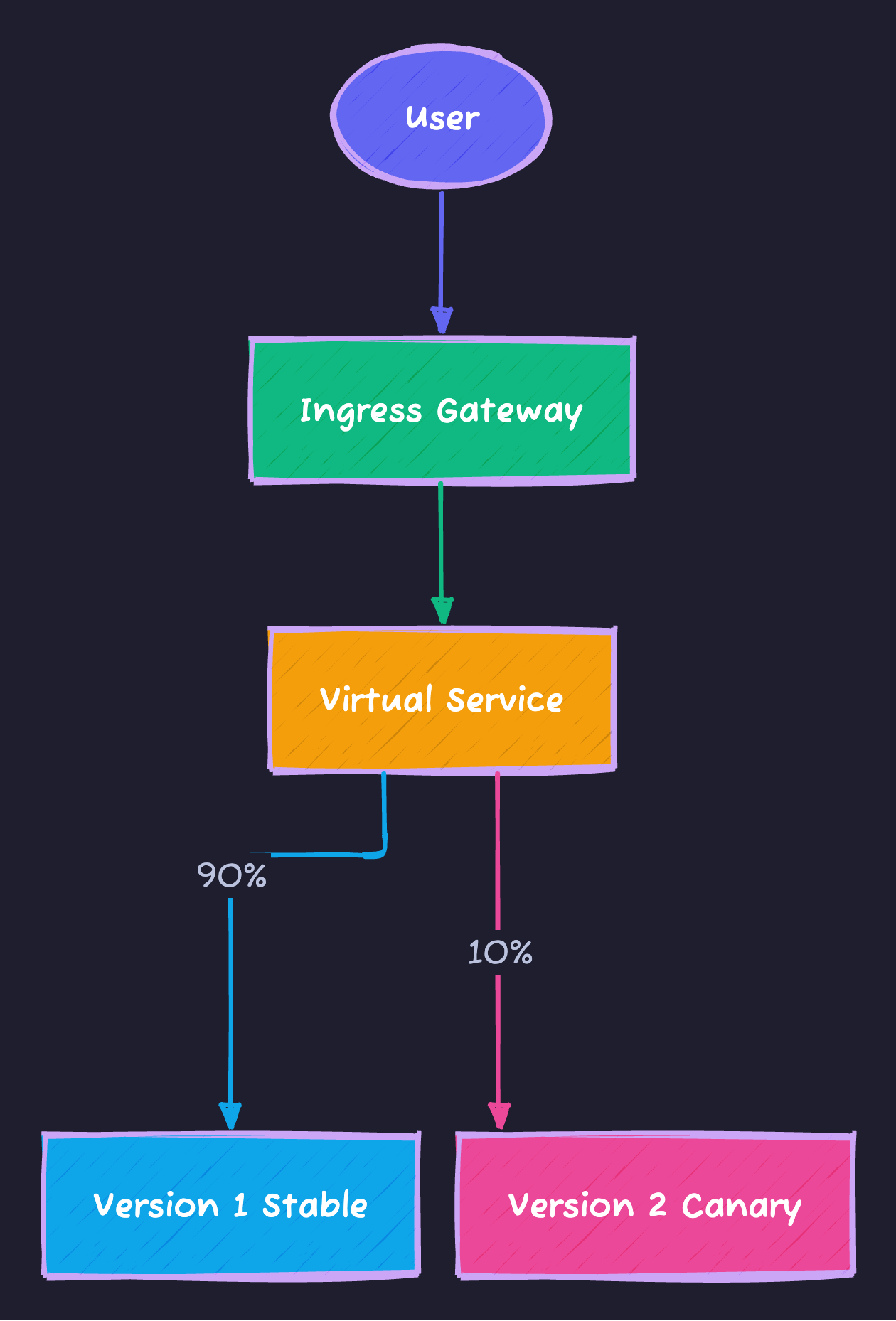
simple: LEAST_CONNCanary Deployments
We can split traffic between versions (e.g., 90% to stable, 10% to canary) without changing code.
apiVersion: networking.istio.io/v1beta1
kind: VirtualService
metadata:
name: my-service
spec:
hosts:
- my-service
http:
- route:
- destination:
host: my-service
subset: v1
weight: 90
- destination:
host: my-service
subset: v2
weight: 10A/B Testing
apiVersion: networking.istio.io/v1beta1
kind: VirtualService
metadata:
name: my-service
spec:
hosts:
- my-service
http:
- match:
- headers:
x-user-type:
exact: "beta"
route:
- destination:
host: my-service
subset: v2
- route:
- destination:
host: my-service
subset: v1Request Routing
apiVersion: networking.istio.io/v1beta1
kind: VirtualService
metadata:
name: my-service
spec:
hosts:
- my-service
http:
# Route by URI
- match:
- uri:
prefix: "/api/v2"
route:
- destination:
host: my-service
subset: v2
# Route by header
- match:
- headers:
end-user:
exact: "jason"
route:
- destination:
host: my-service
subset: v2
# Default route
- route:
- destination:
host: my-service
subset: v1Resilience
Timeouts and Retries
apiVersion: networking.istio.io/v1beta1
kind: VirtualService
metadata:
name: my-service
spec:
hosts:
- my-service
http:
- route:
- destination:
host: my-service
timeout: 10s
retries:
attempts: 3
perTryTimeout: 3s
retryOn: gateway-error,connect-failure,refused-streamCircuit Breaker
apiVersion: networking.istio.io/v1beta1
kind: DestinationRule
metadata:
name: my-service
spec:
host: my-service
trafficPolicy:
outlierDetection:
consecutive5xxErrors: 5
interval: 30s
baseEjectionTime: 30s
maxEjectionPercent: 100
minHealthPercent: 0Fault Injection
apiVersion: networking.istio.io/v1beta1
kind: VirtualService
metadata:
name: my-service
spec:
hosts:
- my-service
http:
- fault:
delay:
percentage:
value: 10
fixedDelay: 5s
abort:
percentage:
value: 5
httpStatus: 500
route:
- destination:
host: my-serviceRate Limiting
apiVersion: networking.istio.io/v1beta1
kind: EnvoyFilter
metadata:
name: rate-limit
spec:
workloadSelector:
labels:
app: my-service
configPatches:
- applyTo: HTTP_FILTER
match:
context: SIDECAR_INBOUND
listener:
filterChain:
filter:
name: envoy.filters.network.http_connection_manager
patch:
operation: INSERT_BEFORE
value:
name: envoy.filters.http.local_ratelimit
typed_config:
"@type": type.googleapis.com/udpa.type.v1.TypedStruct
type_url: type.googleapis.com/envoy.extensions.filters.http.local_ratelimit.v3.LocalRateLimit
value:
stat_prefix: http_local_rate_limiter
token_bucket:
max_tokens: 100
tokens_per_fill: 100
fill_interval: 60s
filter_enabled:
runtime_key: local_rate_limit_enabled
default_value:
numerator: 100
denominator: HUNDREDSecurity
Mutual TLS
# Enable strict mTLS
apiVersion: security.istio.io/v1beta1
kind: PeerAuthentication
metadata:
name: default
namespace: istio-system
spec:
mtls:
mode: STRICT# Permissive mode for specific namespace
apiVersion: security.istio.io/v1beta1
kind: PeerAuthentication
metadata:
name: default
namespace: legacy
spec:
mtls:
mode: PERMISSIVEAuthorization Policies
# Deny all by default
apiVersion: security.istio.io/v1beta1
kind: AuthorizationPolicy
metadata:
name: deny-all
namespace: default
spec:
{}# Allow specific access
apiVersion: security.istio.io/v1beta1
kind: AuthorizationPolicy
metadata:
name: allow-frontend
namespace: default
spec:
selector:
matchLabels:
app: backend
action: ALLOW
rules:
- from:
- source:
principals: ["cluster.local/ns/default/sa/frontend"]
to:
- operation:
methods: ["GET", "POST"]
paths: ["/api/*"]JWT Authentication
apiVersion: security.istio.io/v1beta1
kind: RequestAuthentication
metadata:
name: jwt-auth
namespace: default
spec:
selector:
matchLabels:
app: my-service
jwtRules:
- issuer: "https://auth.example.com"
jwksUri: "https://auth.example.com/.well-known/jwks.json"
audiences:
- "my-service"
forwardOriginalToken: trueapiVersion: security.istio.io/v1beta1
kind: AuthorizationPolicy
metadata:
name: require-jwt
namespace: default
spec:
selector:
matchLabels:
app: my-service
action: ALLOW
rules:
- from:
- source:
requestPrincipals: ["https://auth.example.com/*"]
when:
- key: request.auth.claims[groups]
values: ["admin"]Ingress Gateway
apiVersion: networking.istio.io/v1beta1
kind: Gateway
metadata:
name: my-gateway
spec:
selector:
istio: ingressgateway
servers:
- port:
number: 80
name: http
protocol: HTTP
hosts:
- "*.example.com"
- port:
number: 443
name: https
protocol: HTTPS
tls:
mode: SIMPLE
credentialName: example-credential
hosts:
- "*.example.com"apiVersion: networking.istio.io/v1beta1
kind: VirtualService
metadata:
name: my-service
spec:
hosts:
- "app.example.com"
gateways:
- my-gateway
http:
- match:
- uri:
prefix: "/api"
route:
- destination:
host: api-service
port:
number: 8080
- route:
- destination:
host: web-service
port:
number: 80Observability
Distributed Tracing
# Enable tracing
apiVersion: install.istio.io/v1alpha1
kind: IstioOperator
spec:
meshConfig:
enableTracing: true
defaultConfig:
tracing:
sampling: 100.0
zipkin:
address: zipkin.istio-system:9411Custom Metrics
apiVersion: telemetry.istio.io/v1alpha1
kind: Telemetry
metadata:
name: namespace-metrics
namespace: default
spec:
metrics:
- providers:
- name: prometheus
overrides:
- match:
metric: REQUEST_COUNT
tagOverrides:
response_code:
operation: UPSERTAccess Logging
apiVersion: telemetry.istio.io/v1alpha1
kind: Telemetry
metadata:
name: mesh-default
namespace: istio-system
spec:
accessLogging:
- providers:
- name: envoyDebugging
# Check proxy status
istioctl proxy-status
# Analyze configuration
istioctl analyze
# Debug specific pod
istioctl proxy-config cluster <pod-name>
istioctl proxy-config route <pod-name>
istioctl proxy-config listener <pod-name>
# Check Envoy config
istioctl proxy-config dump <pod-name>
# View metrics
kubectl exec -it <pod-name> -c istio-proxy -- pilot-agent request GET statsSummary
| Feature | Resource |
|---|---|
| Routing | VirtualService |
| Load Balancing | DestinationRule |
| Gateway | Gateway |
| mTLS | PeerAuthentication |
| Authorization | AuthorizationPolicy |
| Observability | Telemetry |
Istio provides comprehensive service mesh capabilities for securing and managing microservices on Kubernetes.
Advertisement
Moshiour Rahman
Software Architect & AI Engineer
Enterprise software architect with deep expertise in financial systems, distributed architecture, and AI-powered applications. Building large-scale systems at Fortune 500 companies. Specializing in LLM orchestration, multi-agent systems, and cloud-native solutions. I share battle-tested patterns from real enterprise projects.
Related Articles
Kubernetes Helm Charts: Package and Deploy Applications
Master Helm for Kubernetes deployments. Learn chart creation, templates, values, dependencies, and best practices for production applications.
DevOpsArgoCD: GitOps Continuous Delivery for Kubernetes
Master ArgoCD for Kubernetes deployments. Learn GitOps principles, application management, sync strategies, and automate your deployment pipeline.
DevOpsKubernetes for Beginners: Complete Guide to Container Orchestration
Learn Kubernetes from scratch. Understand pods, deployments, services, and how to deploy your first application to a Kubernetes cluster with practical examples.
Comments
Comments are powered by GitHub Discussions.
Configure Giscus at giscus.app to enable comments.